Key Points
- 0DIN’s public disclosures corpus is now distributed weekly as a versioned JSONL dataset, with 0din.ai/disclosures remaining the authoritative source and mirrored on Hugging Face and the Mozilla Data Collective to support AI security research.
- The dataset includes general disclosure metadata such as vulnerability type, affected model, researcher attribution, and risk summaries to provide high level context for each finding.
- A vetted subset contains actionable threat intelligence, including triggering prompts, confirmed exploit responses, sector specific variations, and detection signatures for building and testing defenses.
- Each weekly export follows a typed schema with timestamped manifests and publisher git SHA to ensure reproducibility and reliable ingestion into research and security pipelines.
- Organizations can use the enriched subset of disclosures in the 0DIN Threat Feed to operationalize these findings and strengthen real time detection and response against emerging AI model exploits.
0DIN Public Disclosures: Weekly Dataset Distribution
The 0DIN public disclosures corpus is now distributed as a weekly, versioned JSONL dataset. While 0din.ai/disclosures remains the authoritative source, we are mirroring the data to Hugging Face and the Mozilla Data Collective to better support AI security research and evaluation.
Distribution Hubs
-
Hugging Face:
0dinai/public-disclosures - Mozilla Data Collective: Open AI Corpus
Explore AI security with the Scanner Datasheet
The datasheet offers insight into the challenges and solutions in AI security.
Download Datasheet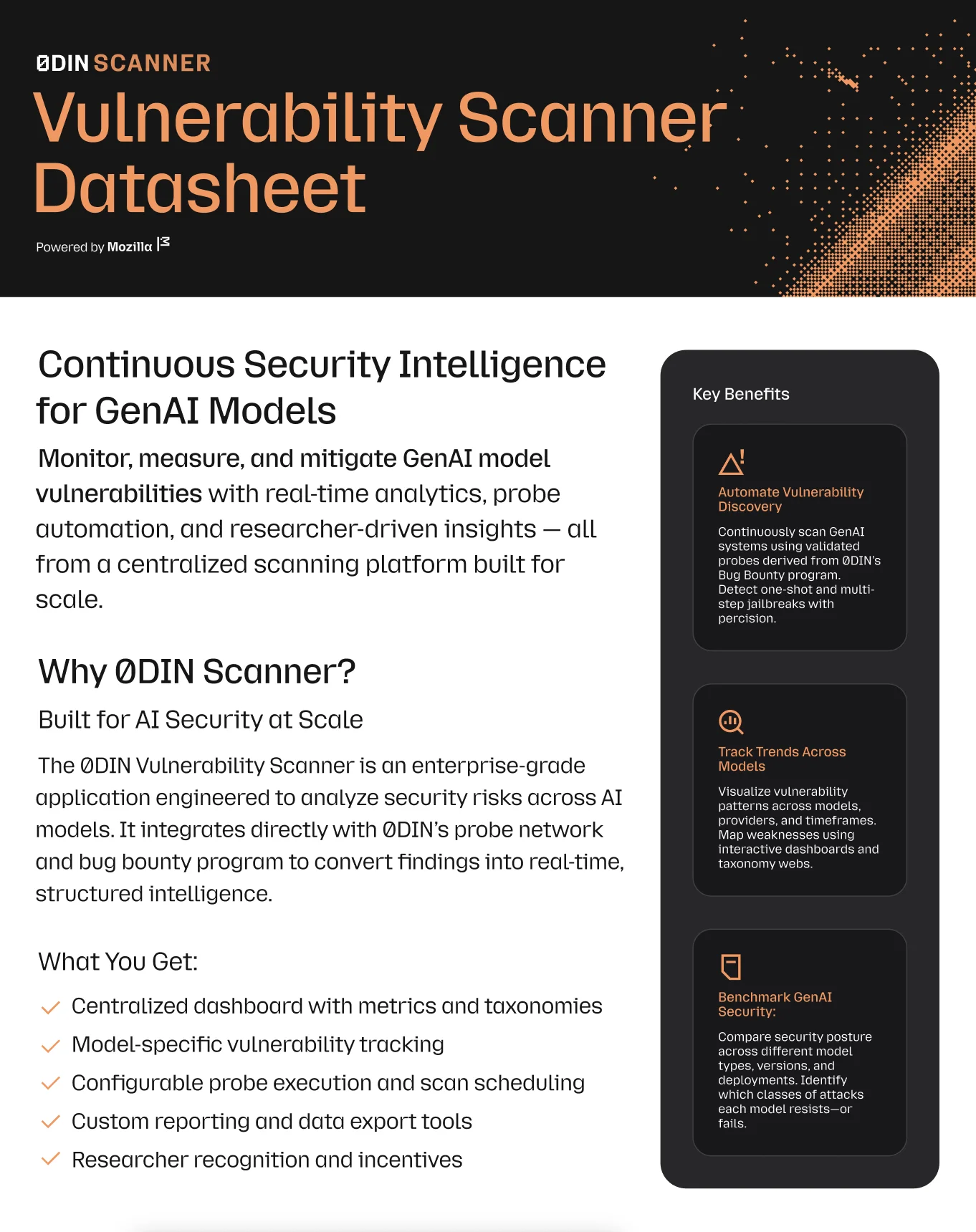
Dataset Structure
The dataset contains two tiers of information, categorized by whether the disclosure has been approved for full technical release.
1. General Disclosures (Metadata)
The majority of records provide the high-level context of a vulnerability. This includes:
- Vulnerability Type & Model: What was found and where.
- Attribution: The researcher responsible for the discovery.
- Summary: A description of the risk and impact.
2. Actionable Threat Intelligence (Full Payloads)
Records approved for the threat-feed subset include additional technical data required to build and test defenses:
- Triggering Prompts: The specific inputs used to surface the vulnerability.
- Target Responses: The resulting model output that confirmed the exploit.
- Sector-Specific Variations: Alternative versions of the prompt tailored for different industries (e.g., medical vs. financial contexts).
- Detection Signatures: The logic and patterns used to identify these exploits in production traffic.
Safeguard Your GenAI Systems
Connect your security infrastructure with our expert-driven vulnerability detection platform.
Technical Specs
To ensure reproducibility in research pipelines, every weekly export includes:
- Typed Schema: A consistent structure for automated ingestion.
- Manifests: Every run is timestamped and carries the publisher's git SHA.
- Format: Versioned JSONL for easy compatibility with standard data science tools.
Roadmap
The subset of records containing full technical payloads is currently a small, vetted allowlist. This set will grow as more disclosures clear the 0DIN review process and are upgraded in the weekly export.
License: CC-BY-4.0
Contact: 0din@mozilla.com